Radio Modem WiFi 6 | optional 5G | Serial | Ethernet | USB
Overview
- WLAN client for 802.11a/b/g/n/ac/ax via 2.4 + 5 GHz WLAN WiFi 6, data rate up to 2,402 MBit/s
- Variant 5G: Worldwide 3G/4G/5G in multi-mode, date rates up to 3.3 Gbps download/900 Mbps Upload
- Integrated OpenVPN client
- Bridge modes for connecting LAN clients: NAT / Single Client NAT / Single Client Cloning / Level 2 Bridge / MWLC Mode
- WEP, 802.11i WPA-WPA2-WPA3-AES-TKIP-PSK
- WPA Enterprise 802.1x PEAP LEAP TLS TTLS
- Certificate management for the authentication via 802.1x
- SCEP (Simple Certificate Enrollment Protocol)
- MQTT (Message Queuing Telemetry Transport)
- 2x Gigabit LAN interfaces
- 1x serial interface: RS232, Serial-Client via TCP/UDP
- 1x USB 2.0 interface, also for additional interfaces
- 1x switching relay controllable via network (e.g. to wake up vehicles from sleep mode)
- Voltage supply 10-60V or via PoE (LAN)
- Robust aluminum housing with various mounting options and screwable connectors
- Configuration via the internal web server, REST-API or with the help of the dedicated MC-Config program
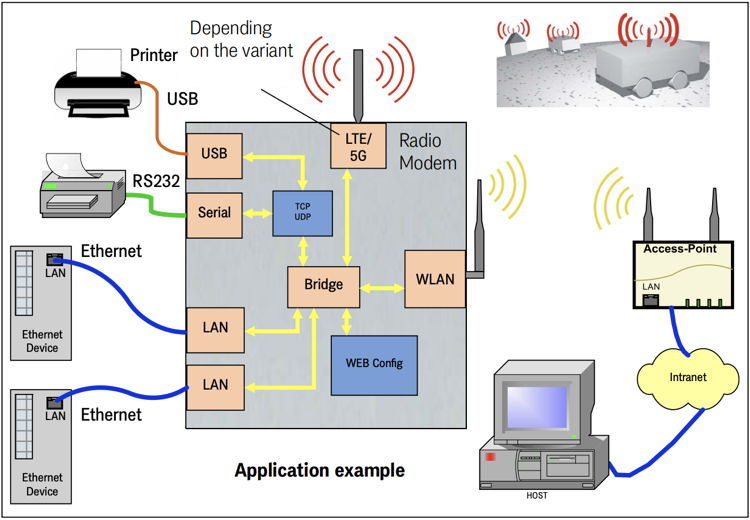 Application example Radio Modem HG G-76354ZA 5G
Application example Radio Modem HG G-76354ZA 5GThe radio modem HG G-76354-A connects devices that communicate via Ethernet or serial interfaces with other networks via WLAN, and in the 5G variant also via mobile networks (see table Variant overview on the back). This includes applications with mobile vehicles such as forklifts or AGV.
The communication partners can be additional radio modems or computers that communicate via a suitable application. Furthermore, extensions are possible via the USB port, which offer additional serial or I/O interfaces, for example.
Variants
The radio modem is available in different variants. The differences are the casing and the number of available interfaces. All variants can use the firmware file and can be configured with the MC-Config program attached at the bottom of this page.
- HG G-76354XA: Top hat rail mounting narrow side
- HG G-76354XA 5G: Casing like XA with option 5G
- HG G-76354YA: Top hat rail mounting long side
- HG G-76354YA 5G: Casing like YA with option 5G
- HG G-76354ZA: Flange casing
- HG G-76354ZA 5G: Casing like ZA with option 5G
Security Notes
- Firmware 3.14: All firmware versions of line 3.14 contain security relevant updates related to line 3.14, see also complete Changelog. The firmware must be kept up to date.
Open Source Compliance Information
The firmware of the radio modems described on this page includes software code developed by third parties under the GNU General Public License ("GPL") or GNU Lesser General Public License ("LGPL"). More information about the terms of use and how to access the GPL code and LGPL code used in this product can be found on our Open Source page.
Downloads
| Attachment | Filesize – | Uploaded |
|---|---|---|
| 2.85 MB | 09.08.2023 | |
| 2.59 MB | 18.12.2023 | |
| 38.34 MB | 26.04.2024 | |
| 464.74 KB | 26.04.2024 |

